- Columbus: (614) 702-7700
- Cleveland: (216) 393-2484
- Akron/Canton: (330) 685-9100
CMMC 2.0 Changes – The Impact on DoD Contractors
Overview
On November 4, 2021, the DoD announced CMMC 2.0, the latest iteration of its new Cybersecurity & Compliance Framework for its contractors, and also the Defense Industrial Base (DIB) which introduced significant changes to the CMMC program it had started rolling out with the pilot contracts in early 2021. Feedback from the industry and small businesses was given consideration to make these changes.
There are notable changes in these four areas:
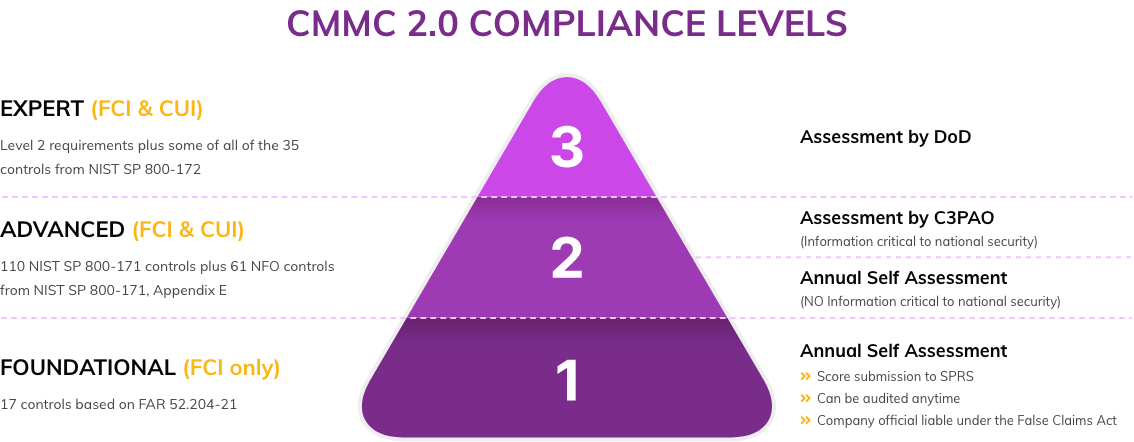
1. CMMC 2.0 Levels
To simplify the requirements, the different CMMC Certification Levels were reduced from five down to three. Levels 2 and 4 from CMMC 1.02 were eliminated. Similar to the earlier version, CMMC 2.0 Level 1 is limited to the handling of Federal Contract Information (FCI) while CMMC 2.0 Level 2 (former Level 3) allows the handling of FCI and Controlled Unclassified Information (CUI). The new CMMC 2.0 Level 3 combines the old Levels 4 and 5, and will only apply to a small set of companies. For more in-depth information, see our CMMC 2.0 Compliance Levels page.
2. CMMC 2.0 Control Requirements
Overall, the control requirements have been scaled back to or close to the 110 controls in NIST SP 800-171.
-
CMMC 2.0 Level 1 Controls – Foundational Level
No changes have been made as compared to CMMC 1.02. 17 processes need to be implemented to fulfill this Foundational Level 1.
-
CMMC 2.0 Level 2 Controls – Advanced Level
The Control requirements were scaled back to the 110 controls of NIST SP 800-171 which were a requirement under DFARS 252.204-7012 (since 1.1.2018) and DFARS -7019 (since 11/30/2020) already. The planned additional 20 controls unique to CMMC 1.02 were eliminated.
The bottom line is that under CMMC 2.0, this “Advanced” level will be equivalent to the NIST SP 800-171. The requirements regarding documentation (policies, procedures, etc.) are not explicitly mentioned any longer which might lead some to conclude that no documentation is needed any longer. However, a solid documentation was always required for a NIST SP 800-171 implementation as well so this doesn’t represent a change.
-
CMMC 2.0 Level 3 Controls – Expert Level
In addition to the requirements from Level 2, CMMC 2.0 Level 3 will be based on a subset of NIST SP 800-172 requirements. This “Expert” level is currently under development.
3. CMMC 2.0 Assessment Requirements
Probably the most controversial revision is regarding the changes to the assessment requirements. Only contractors of Level 3 and part of Level 2 will have to become certified. Those in Level 1 and the remainder of Level 2 will be allowed to perform self-assessments.
-
CMMC 2.0 Level 1 Assessments
Contractors that will handle FCI exclusively (Level 1) will no longer be required to become certified. Instead, they must provide an annual Level 1 self-assessment with an additional annual affirmation from a senior company official that the company is meeting requirements. The score of the self-assessment should be submitted to the Supplier Performance Risk System (SPRS) as well.
-
CMMC 2.0 Level 1 Assessments
This “Advanced” Level allows for managing CUI and is unique in the sense that the organizations required to achieve this compliance level are divided into two subsets — resulting in two different assessment requirements. The criterion that is used to categorize contractors into one of the subsets is if the information they handle is “critical to national security” or not. This will need to be clarified further by the DoD.
Level 2 – Subset 1:
Contractors that handle information that is NOT deemed critical to national security. These organizations can perform the annual self-assessments as the companies in Level 1.
Level 2 – Subset 2:
Contractors managing information deemed critical to national security. These companies will have to be certified and will be assessed by a Third-Party Assessment Organization (C3PAOs) which will be accredited by the CMMC-AB.
-
CMMC 3.0 Level 1 Assessments
Organizations in the “Expert” level will have to become certified. At this level, the certification assessment will be performed by government officials.
4. CMMC 2.0 PoA&M requirements
The initial version, CMMC 1.02, did not allow for any open items in the Plan of Actions and Milestones (PoA&M) document. The DoD currently softened its stance and intends to allow companies to receive contract awards with a Plan of Actions and Milestones (POA&M) in place to complete CMMC requirements. However, only low-risk items are allowed to be as open items on the list, and there is a 180-day period in which the contractor will have to remediate the issue and become compliant. Another additional requirement is the minimum assessment scores. All the highest weighted NIST SP 800-171 controls will have to be implemented without exceptions at contract award.
Waivers
The DoD is considering CMMC waivers but made it clear that these would be issued on a very limited basis for select mission-critical instances and require approval from senior DoD leadership. The waivers have a limited duration and need to be supported by mitigation strategies to reduce the risk to the CUI handled by the contractor.
Timeline
All these changes impact the CMMC implementation timeline and rollout which had started in early 2021 and will end on October 31, 2025, as mentioned in DFARS 252.204-7021. Currently, CMMC 2.0 is in the rulemaking process which is expected to take 9-24 months.
The DoD stated that it will not include CMMC requirements in contracts until this process has been finalized. CMMC will be part of new DoD contract requirements once completed. Considering that the implementation of CMMC requirements can take several months, the time to start the journey towards CMMC compliance is now.

